00:00:20.080
Now, on to our penultimate talk. It's my second favorite word.
00:00:27.359
Our speaker, Steve Klabnik, is someone who's been programming for 20 years, since long before he ever had to shave.
00:00:34.160
He still doesn't have to shave, to be honest. He's been doing Ruby for six years and is one of the most dedicated open source supporters I know.
00:00:41.840
Steve suffers for your good; he is a Rails committer, though not a Rails core member. Today, I asked Steve to deliver a talk that would be a little different for you.
00:00:48.559
I don't know how much code he's going to show you; probably none. But he will talk to you about some issues that I believe we all care about. Thank you, Steve.
00:01:23.920
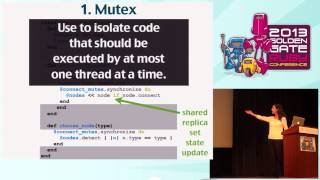
Hi everybody, I'm Steve. I will let you know that my amazing ThinkPad X1 Carbon worked on this projector on the first try, so Linux is good!
00:01:30.479
I took a lot of crap for switching away from Mac, so anyway, this talk is called "No Secrets Allowed: You, Me, and the NSA Makes Three."
00:01:36.400
Basically, I want to share some insights about security and privacy and how these issues have affected all of us.
00:01:42.640
And more importantly, why they affect us all. I know a lot of people think, "Steve, you're the resident crazy person who cares about security stuff."
00:01:48.000
You're the oddball who's using Linux because you don't want to use proprietary software. So, please explain all the stuff I need to know about these issues.
00:01:59.840
I decided that this would be a good candidate for a talk to shake it up a little, and also so I could later point people to the URL instead of having to explain everything all the time.
00:02:12.160
So let's discuss this. There are basically three parts to this talk. The first one is what is the current state of reality. A lot of people don't appreciate what reality is at the moment.
00:02:23.599
Then we'll discuss the tools we have in this reality and how they allow us to shape the current situation. Finally, what do we do from here? Where do we go? How should we think about these problems?
00:02:35.599
And what should we do with the stuff we learned? Those are the three parts of the talk.
00:02:41.519
First of all, let's have a reality check. This privacy issue has been in the news a lot lately.
00:02:47.280
I will specifically address the NSA issues that have been coming out due to recent events over the last year.
00:02:53.920
As someone who has cared a little bit about privacy, I admit I haven’t always prioritized it. I’ve used Macs for a long time, and while I don’t think they are inherently insecure, I’ve often traded security for convenience.
00:03:06.080
This is not a talk about how I know everything on this topic while you all don't. I only started paying attention when these recent scandals occurred.
00:03:12.080
But as someone who is generally privacy-focused and a little anti-NASA, FBI, CIA, I find it frustrating that for years people have said things like, "The government can read your stuff on the Internet." And people dismissed it by saying, "Yeah, whatever, you're nuts."
00:03:30.319
Then leaks come out proving that the government has been reading everything on the Internet, and suddenly everyone says, "Oh, that's old news; it's been happening forever." It's exasperating! While it’s frustrating, they are actually right.
00:03:48.400
I want to start by sharing some history about what our government has done in your name and mine. Apologies to friends not from the U.S. I’m going to lump everyone together, as that’s what we tend to do here in the U.S.
00:04:10.319
I mention this because some South American friends have actually appreciated that I say 'the States' instead of 'America' since they, too, are Americans.
00:04:15.680
So in this first wave of history, I want to share a chunk of Google Maps. This line here is where we currently are, and according to Google Maps, it’s about a 17-minute walk to what’s essentially the corner of Second and Folsom.
00:04:34.639
This is a building that, for a long time, nobody thought that much of, but that has since become somewhat terrifying. Brutalism is a style that stands out, right? This building has no windows, and people just come in and out.
00:04:49.760
Inside this building, there’s a room, I believe it’s 641A, where a technician was working. One day, he walked in and thought, "Huh, this is strange; what's this doing here?"
00:04:56.320
What he found turned out to be classified, and he was subsequently sued after coming out about it, leading to a huge court case where all of this information came to light.
00:05:05.760
What was installed there was something called a fiber optic splitter. Essentially, this technology does not mean that half of the data goes one way and half goes another.
00:05:19.600
This is about copying; it sends a full copy of the data to one place while still sending another full copy to the intended recipient.
00:05:30.720
Many people know that SOMA has become important for internet companies as a connection point. It’s questionable at best to think about someone potentially spying and keeping a copy of all data flowing through this area.
00:05:41.039
This was occurring back in 2001, and though many people freaked out over this incident, eventually, apathy set in. This is just one prominent incident, but there’s a history of terrible things happening, particularly in the 70s, relating to something called COINTELPRO.
00:06:01.039
COINTELPRO is an abbreviation for Counter Intelligence Program, and it was a series of shady behaviors conducted by the FBI and CIA under the guise of national security.
00:06:13.440
The terrible things included monitoring, infiltrating, and disrupting groups that the FBI considered subversive. This included any communists, socialists, and people involved in the Civil Rights Movement.
00:06:27.599
People fighting for racial equality, those in the National Lawyers Guild working with dissidents, and various independent political groups were surveilled by the government.
00:06:44.640
Even Albert Einstein, who was a staunch socialist, was monitored. It’s disturbing to think of the kind of intimidation tactics used; for example, they even mailed a letter to Dr. Martin Luther King, encouraging him to kill himself.
00:07:01.040
Most of the information about these surveillance practices eventually came out because of FOIA laws. Out of interest, the resources of COINTELPRO were utilized 85% against people advocating for equality.
00:07:10.160
Only a mere 15% were used to monitor white supremacy groups like the KKK. It’s quite a shocking statistic and reflects the systemic injustices present.
00:07:26.480
A notable example is Eleanor Roosevelt; as the first First Lady, once the NSA was formed, they compiled a 3000-page document on her due to her involvement in the Civil Rights Movement. Frank Sinatra also had an extensive file, largely due to his frequent travel.
00:07:45.040
Similarly, Marilyn Monroe had one, and John Lennon found himself in the radar as well, where they tried to see if they could deport him. The Beatles, as a group, also had a separate dossier.
00:08:01.760
These files show extensive documentation of surveillance conducted against individuals who were merely advocating for social justice or challenging the status quo. Most notably, Barry Goldwater was also subject to spying, making the social climate of that time highly suspicious.
00:08:18.080
One other casualty of the paranoia was Dr. Seuss, who was investigated amidst concerns he might be a communist. This is merely a small example of the digital and historical surveillance that has faced activists.
00:08:35.840
The Church Committee, which met in the 70s, revealed shocking details about the CIA. They uncovered that a quarter of a million letters were opened and photographed at the post office between 1953 and 1973.
00:09:06.560
There were lists cataloging individuals who would be rounded up during a national emergency—26,000 people! Think about that for a moment; it raises profound moral questions about surveillance and security.
00:09:32.800
These examples are just snippets of history painting a dismal picture of government oversight. I understand the collection of the current events information can be complex. If you're unfamiliar, search for the 2013 Mass Surveillance Disclosures on Wikipedia.
00:10:01.760
The leaked information is crucial in understanding the extent of surveillance that has taken place. I hesitate to label it merely as 'the Snowden stuff,' as it’s less about the leaker and more about the implications of what was disclosed.
00:10:18.560
There are several key points I want you to take away. First, any byte that leaves your computer unencrypted is basically public. For instance, logging into your webmail without SSL makes you vulnerable.
00:10:41.760
Second, the phrase 'I have nothing to hide' signifies that one may be under-informed on this issue. Privacy and security affect all of us, regardless of whether we think they do.
00:11:03.200
And lastly, cell phones can be seen as spy devices. Many wonder why I still use an iPhone when I care about privacy. My first answer is personal preference, but the truth is, both Android and iPhones have vulnerabilities.
00:11:16.480
Smartphones are structured in a way that they continuously ping the closest tower to use cellular networks, including location data. This makes them insecure by design, as evidence shows that governments can get access to your microphone.
00:11:28.480
There are many instances of the government using these methods to gather intelligence, which are often revealed during court cases. To sum it up, if it leaves your computer unencrypted, someone can intercept it, and your phone is a constant surveillance device.
00:11:54.080
Now let’s talk a little about metadata—the data about data. Metadata is potentially more dangerous than plain content.
00:12:00.880
In the context of HTTP, this includes headers, which provide insight into where a request is going. It’s similar with phones; the call logs reveal whom you're contacting.
00:12:19.600
What you’re saying isn’t always as significant as who you are contacting and when. That context could reveal more than we think, and it can affect innocent people based on appearances.
00:12:38.080
Governments argue that metadata surveillance isn’t dangerous while suggesting it’s crucial for counter-terrorism efforts. This contradiction is unsettling and needs addressing within the public sphere.
00:12:53.440
An example of the power of metadata can be gathered from some leaked documents, which depicted a program analyzing who interacts with whom, determining who to target for significant actions.
00:13:07.440
We see how innocent individuals can be placed under a spotlight of suspicion merely from metadata patterns—those who correlate with ‘shady’ individuals can get caught in the crosshairs, regardless of their actual activities.
00:13:30.560
Further, there have been troubling stories of familial trust dissolving under the harsh spotlight of data analysis, such as a father discovering his daughter’s pregnancy due to Target ads.
00:13:43.840
In another case, Facebook might know about a user’s sexual orientation before they do, based solely on metadata. These insights into someone's life can have dire ramifications, particularly for individuals in unsupportive environments.
00:14:01.760
As we move forward, I will share two tools we can use. The first one is Tor. For those interested in navigating these issues, Tor can be a useful asset.
00:14:14.080
I will mention that no tool is perfect, and each comes with a set of drawbacks alongside benefits.
00:14:24.000
Tor works through a process where you can connect securely through a network of volunteer-operated servers, masking your original IP address and enhancing your anonymity online.
00:14:44.560
Here’s how it works: your Tor client first retrieves the list of Tor nodes and then forms an encrypted connection through at least three relays. This design ensures that no single point of the network knows both the sender and recipient.
00:15:05.040
While Tor protects against metadata logging, if you log into your Facebook account while using it, you would still have vulnerabilities related to account access.
00:15:19.600
Another important thing to keep in mind is that Tor doesn't protect you from surveillance in the sense that government agencies can analyze traffic patterns and may identify users.
00:15:33.760
The second tool that I want to discuss is GPG, which stands for GNU Privacy Guard. GPG allows users to create encrypted messages or files to maintain privacy.
00:15:54.880
In order to understand GPG, you need to grasp the distinction between public and symmetric key encryption.
00:16:07.040
GPG functions based on a public and a private key pair. So, if you want to send a recipient a secure message, you encrypt your message using their public key.
00:16:29.840
They are then the only one who can decrypt the message with their private key. This allows for secure communication across the internet.
00:16:44.000
It’s also possible to sign your messages using your private key, proving that the message indeed came from you.
00:16:57.440
The downside is that trusting that the public key you obtain corresponds to the actual person can be a challenge, because people can create fake keys.
00:17:11.040
Establishing a web of trust through key-signing events, where mutual acquaintances validate each other's keys, can help combat this issue.
00:17:25.760
Some people have been talking about running key-signing parties at conferences, which would allow the community to establish trust.
00:17:38.080
Ultimately, GPG is powerful if utilized correctly, but the effectiveness relies on widespread use among your contacts.
00:17:55.520
It's essential that the people you wish to communicate with also adopt these practices for meaningful secure conversations.
00:18:07.680
Thus, even if everyone starts sending encrypted emails that are not perfect, it helps everyone involved and reduces the stigma surrounding secure communication.
00:18:26.080
Speaking of that, we need to acknowledge the UX and UI issues prevalent in many security applications.
00:18:41.600
If I ever wanted to generate a new GPG key, the command-line interface can be daunting—even asking technical users complex pathways to establish keys.
00:18:54.720
It’s a tedious process and proves challenging for normal users, requiring someone to take charge of helping.
00:19:06.560
Not to mention the better options available; the Tor browser bundle simplifies the Tor experience for average users, allowing you to surf the web privately with a click of a button.
00:19:27.680
But we still need to focus on the products we build and the subsequent privacy implications. If we simply continue building massive data-collecting platforms, it's no surprise the government will use those systems against us.
00:19:44.320
So in closing, we need to prioritize understanding and implementing security and privacy in our daily lives. Thank you very much for your time!